On April 12th, the Ukrainian CERT (CERT-UA) reported that the Russian Sandworm Team targeted high-voltage electrical substations in Ukraine using a new variant of a malware known as Industroyer (aka, Crash Override). The Sandworm Team, which is associated with the Russian GRU, previously used the original Industroyer variant to compromise Ukrainian power grids in 2016, causing a portion of Kyiv to lose power for over an hour. The new variant, dubbed Industroyer2, directly interacts with electrical utility equipment to send commands to the substation devices that control the flow of power.

At IronNet, we look to behavioral analytics to detect unknown threats on enterprise networks before adversaries succeed at their endgame: exploitation or exfiltration. First, we do the threat detection groundwork needed to spot abnormal network activity across our customers’ networks. Second, our IronDefense NDR expert system scores these alerts, prioritizing the most interesting events to help cut down on alert fatigue. Finally, we take a Collective Defense approach to crowdsourced threat intelligence sharing in real time.
The May IronNet Threat Intelligence Brief
This ability to analyze and correlate seemingly unrelated instances is critical for identifying sophisticated attackers who leverage varying infrastructures to hide their activity from existing cyber defenses. As reported in the May Threat Intelligence Brief, our analysts review alerts from millions of data flows that are ingested and processed with big data analytics. We apply ratings to the alerts (benign/suspicious/malicious) and immediately share them with IronDome Collective Defense participants.
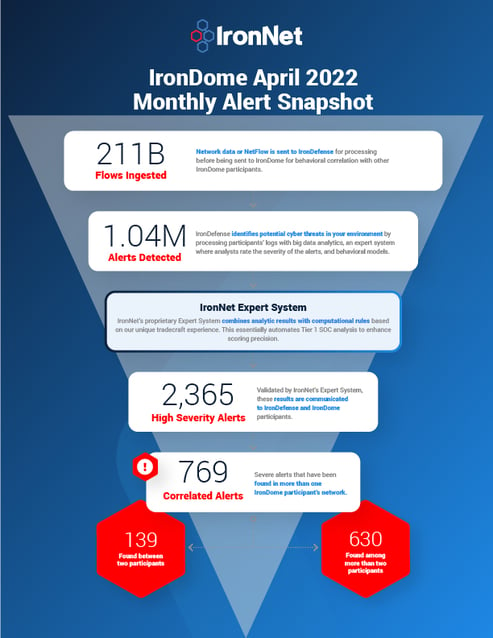
Here is a snapshot of what we discovered across the IronDome communities in April, showing 769 correlated alerts across IronDome participant environments:
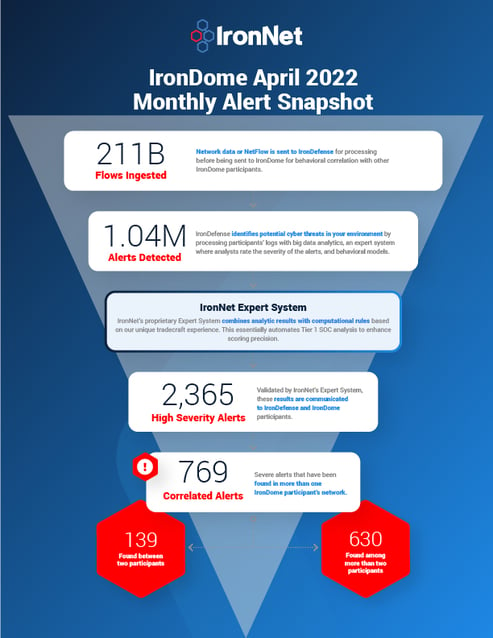
Given the unique cross-sector visibility and Collective Defense capabilities of IronDome, we are able to highlight the most frequent behaviors each month, in turn enabling us to track trends over time. For April, the most frequent behavior analytics were Suspicious File Downloads (734), New and Suspicious Domains (537), and Credential Phishing (213).
Analysis of IoCs
In addition to correlated alerts, significant IronDome community findings revealed 1,174 Indicators of Compromise (IoC) that may pose risk to IronDome participant environments. For example, we analyzed the malicious domain pubfruitlesswording[.]com, which is associated with Terraclicks and may redirect users to suspicious sites that communicate malicious files.
All the IoCs we analyzed are used to trigger alerts that are mapped to the Cyber Kill Chain to identify the stage and progression of the threat. They can be used to create detection rules for network, endpoint, or other security tools currently deployed to mitigate cyber risk in each IronDome participant’s environment.
See the April Threat Intelligence Brief for the full list of recent IoCs.
The bigger picture of Collective Defense
Every month, IronNet’s expert threat analysts create threat intelligence rules (TIR) based on significant community findings from IronDome, malware analysis, threat research, or other methods to ensure timely detection of malicious behavior targeting an enterprise or other IronDome community participants.
In April, we created 2,294 threat intel rules of our 304,714 created to date. Some examples of this month’s research related to indicators associated with malware delivery domains for Cobalt Strike, UNC788, FIN7, and the Russian Gamaredon campaign.
This combination of behavior-driven and IoC signature-based detection, alert ranking, and sharing ensures IronDome participants have the broadest view of threats facing their enterprise.
Industroyer2 cyber attacks
The threat actors planted the malware on systems within a regional Ukrainian energy firm and were believed to have gained access in early February 2022. However, the attack was detected and mitigated before a blackout occurred, which would have impacted roughly two million people. As of right now, the initial access vector and how the threat actors moved laterally from the IT network to the Industrial Control System (ICS) network is not yet known.
You can see the latest industry news in the full brief or check out IronNet’s threat intelligence hub.


.png)