Discovered in January 2022, ChromeLoader is a multi-stage browser hijacker/adware campaign that has impacted various victims around the world. ChromeLoader is a multi-stage malware family, meaning each variant has a similar looking infection chain, such as the use of malicious browser extensions in all of the versions, but also contains different stages throughout each of their infection chains. There are 4 variants (3 windows, 1 macOS). There is Variant 0, which is named that way because it was active before Variant 1 (the first variant discovered in the wild), with its first known attack occurring in December 2021. Then we have Variant 1 that was mainly active in January, Variant 2 that has been active since March, and a fourth MacOS variant that has been active since March as well.
.jpg?width=185&name=FirstPage004%20Collective%20Defense%20Monthly%20Report%202022_July%20(1).jpg)
At IronNet, we look to behavioral analytics to detect unknown threats on enterprise networks before adversaries succeed at their endgame: exploitation or exfiltration. First, we do the threat detection groundwork needed to spot abnormal network activity across our customers’ networks. Second, our IronDefense NDR expert system scores these alerts, prioritizing the most interesting events to help cut down on alert fatigue. Finally, we take a Collective Defense approach to crowdsourced threat intelligence exchange in real time.
The August IronNet Threat Intelligence Brief
This ability to analyze and correlate seemingly unrelated instances is critical for identifying sophisticated attackers who leverage varying infrastructures to hide their activity from existing cyber defenses. As reported in the August Threat Intelligence Brief, our analysts review alerts from millions of data flows that are ingested and processed with big data analytics. We apply ratings to the alerts (benign/suspicious/malicious) and immediately share them with IronDome Collective Defense participants.
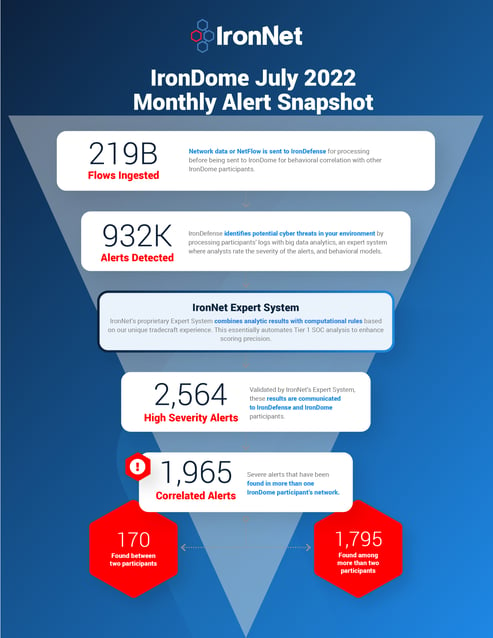
Here is a snapshot of what we discovered across the IronDome communities in July, showing 1,965 correlated alerts across IronDome participant environments:
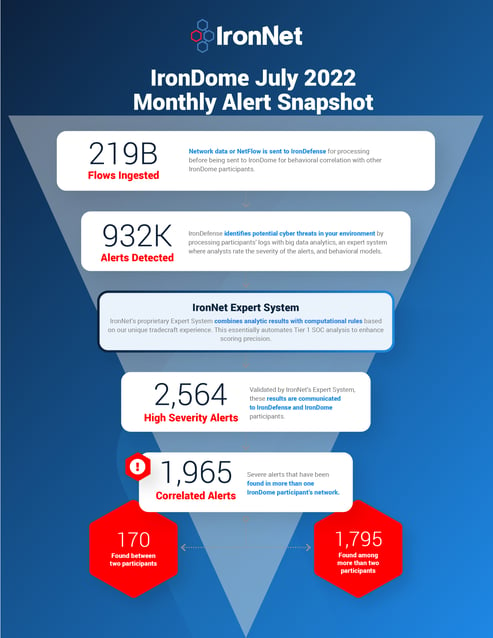
Given the unique cross-sector visibility and Collective Defense capabilities of IronDome, we are able to highlight the most frequent behaviors each month, in turn enabling us to track trends over time. For July, the most frequent behavior analytics were New and Suspicious Domains (273), Credential Phishing (136), and Beaconing (37).
Analysis of IOCs
In addition to correlated alerts, significant IronDome community findings revealed 608 Indicators of Compromise (IOC) that may pose risk to IronDome participant environments. For example, we analyzed the malicious domain suajornadaderiqueza[.]com, a known malicious site that targets enterprise users with Microsoft phishing pages. In the full URL, it appears the targeted enterprise account is base64 encoded at the end. Additionally, when requesting the full URL, the site redirects to https://ai-mfg[.]net, which hosts the actual Microsoft phishing page. This URL seems to include the targeted user email in plain text. Activity should be reviewed and determine whether an enterprise account was targeted.
All the IOCs we analyzed are used to trigger alerts that are mapped to the Cyber Kill Chain to identify the stage and progression of the threat. They can be used to create detection rules for network, endpoint, or other security tools currently deployed to mitigate cyber risk in each IronDome participant’s environment.
See the August Threat Intelligence Brief for the full list of recent IOCs.
The bigger picture of Collective Defense
Every month, IronNet’s expert threat analysts create threat intelligence rules (TIR) based on significant community findings from IronDome, malware analysis, threat research, or other methods to ensure timely detection of malicious behavior targeting an enterprise or other IronDome community participants.
In July, we created 59,043 threat intel rules of our 379,740 created to date. Some examples of this month’s research related to indicators associated with Cobalt Strike beacon payload distribution and C2, IOCs related to Robin Banks phishing kits, and IOCs related to ChromeLoader malware.
This combination of behavior-driven and IOC signature-based detection, alert ranking, and sharing ensures IronDome participants have the broadest view of threats facing their enterprise.
ChromeLoader Malware
The ChromeLoader malware is used for hijacking victims’ browser searches and presenting advertisements, which are two actions that really do not cause serious damage or leak highly sensitive data. However, based on the wide distribution the attackers gained in such a short time, they were able to inflict heavier damage than would be thought with this kind of malware.
You can see the latest industry news in the full brief or check out IronNet’s threat intelligence hub.


.png)

.jpg?width=185&name=FirstPage004%20Collective%20Defense%20Monthly%20Report%202022_July%20(1).jpg)