
Enterprise threat detection is a growing concern. By 2025, a staggering amount of data will be created every day — equivalent to more than 200 million DVDs each day.[1] To traffic much of this data, the cloud remains popular in all formations (hybrid, private, public, boutique), and so do environments for edge and distributed computing such as campuses and small-footprint data centers. Meanwhile the number of small offices and shared workspaces are growing to support today’s popular gig and innovation economy. The common core of all these environments — whether virtual or physical — is the enterprise network. Despite its many benefits as the backbone of the digital economy, the enterprise network has become a breeding ground for sophisticated hackers, many of whom are nation-state level adversaries looking to dwell there in advance of larger attacks.
For any network, the significance of Network Traffic Analysis (NTA) for strengthening cybersecurity is abundantly clear. The importance of advanced NTA, which draws on behavioral analysis to uncover unknown threats, is even greater. It offers a way to balance a fundamental reliance on networks and the potential window they open to relentless, determined hackers. Because the cloud employs the same network architecture as the physical enterprise, the ability to capture raw, virtual network packets is a critical piece of a comprehensive cybersecurity plan.
With this broader threat landscape in mind, IronNet has launched IronNet Virtual Sensor, which complements our family of physical IronSensor products for raw network packet collection. This new cloud implementation allows IronNet to ingest encrypted network traffic for behavioral analysis and threat detection holistically, across both the virtual and physical networks across an enterprise. After all, malicious activity does not know boundaries between the two. A cyber threat can start in the cloud and move to attack the physical network just as easily as if the hackers had started in the physical network from the outset.
Is it just as important to expand Network Traffic Analysis into edge environments, including smaller campus data centers and small-office network closets: anywhere space is limited and hypervisors such as VMware ESX are used to provide services in a smaller physical footprint.
Benefits for any networking environment
The IronNet Virtual Sensor brings another layer of defense to any environment.
Benefits for the private cloud
- The ability to collect and analyze the raw network packets passing through the VLANs between hosted virtual machines
- Collection and analysis of the raw network packets mirrored from the physical network
- No need for additional hardware
- Availability as an OVA for VMWare vSphere: the VIS ESX-01 Virtual Sensor
- Simple installation
[1] CB Insights, “What is edge computing? April 28, 2020. https://www.cbinsights.com/research/what-is-edge-computing/
Benefits for the Amazon Web Service (AWS) public cloud
- Collection and analysis of the raw network packets passing through your AWS instance versus log data generated by AWS
- Availability as an ami with cloud formation script (the VIS-AWS-01 Virtual Sensor)
Benefits for your enterprise network
- Comprehensive network traffic collection, analysis, and detection across the whole enterprise
- A seamless analysis workflow: this lack of boundaries cloud and on-premise means that an alert that is a result of bad activity that crosses from private cloud to enterprise to public cloud will be presented as one alert.
- The same monitoring and management whether using virtual or physical IronSensors
Strategic placement of IronSensors
No two enterprise networks are the same; however, they all depend on packet routing and broadcast. Knowing how the network routes traffic through the core and how the broadcast domains for the edge are built is critical for the strategic placement of IronSensors, whether physical or virtual.
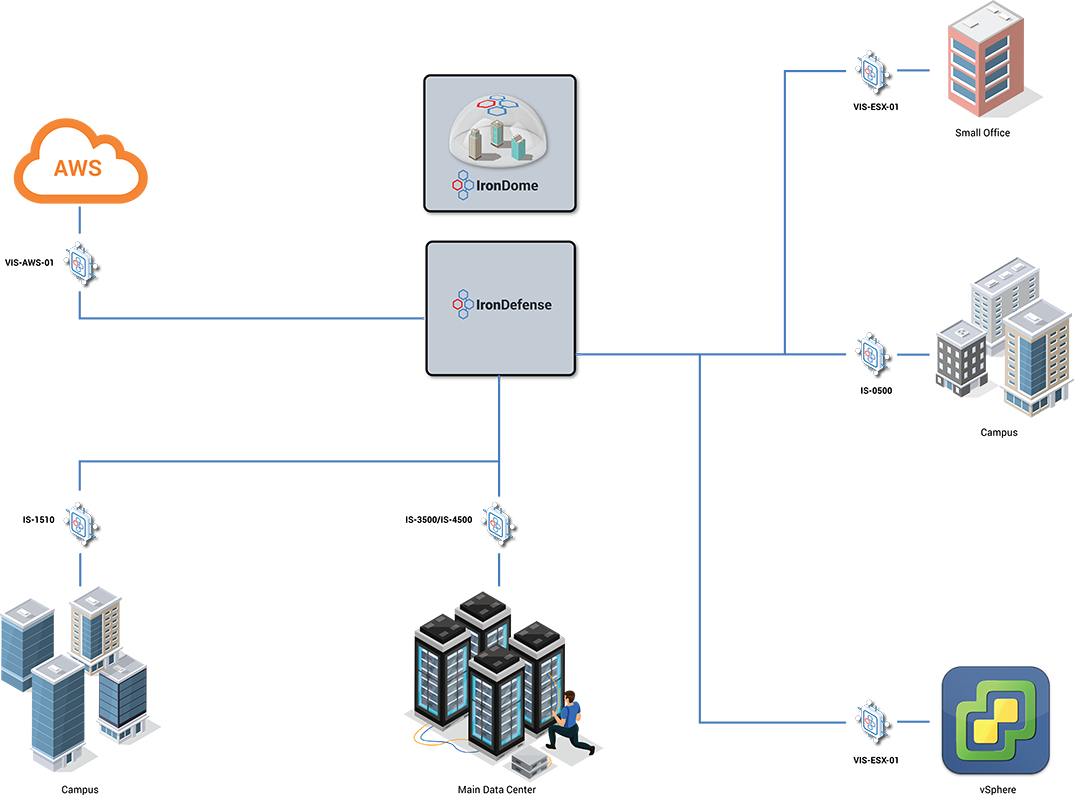
The first question you may have is why an IronSensor for each location? They are needed to ensure complete coverage to detect behavior changes.
Let’s say Mary works in the small office and uses a VM Desktop hosted in the vSphere cloud. The IronSensors in each location will collect the necessary data to establish baseline normal network traffic behavior analyzed in the IronDefense platform, IronNet’s advanced NTA platform. In turn, this data is used to inform the IronDefense analytics applied to the whole office. Later, the AWS sensor (VIS-AWS-01) monitors data between the vSphere and AWS clouds that IronDefense analytics determine is abnormal behavior for another employee, Bill. This holistic architecture for data collection enables IronDefense to generate an alert, in turn notifying the security team of this abnormal network traffic behavior. As it turns out, IronNet’s Collective Defense platform highlighted to the community this change in behavior was occurring across the enterprise, and IronNet quickly blocked the activity across the entire network via a Threat Intelligence Rule.
There are additional benefits for deploying IronSensors across the enterprise network:
- Access to raw network packet, PCAP. Using IronDefense you can hunt across the data to better understand the change in behavior. There is an additional capability to download the PCAP files for storage or examination using tools such as wire shark. Access to this data is controlled using roles and the PCAP files can be downloaded encrypted and password protected.
- Detecting and being notified of known bad activity at the source enables quick action by the security team. IronNet has also announced knowledge-based threat detection and the virtual and physical IronSensor are key. Detecting known threats in real-time, as the raw network traffic is collected, enables IronDefense to alert on a different behavior. Since network traffic patterns for a data center are different from those for a small office, each IronSensor delivers both common and unique functions.
Again, no enterprise network is designed, built, or used the same way. Your IronNet sales team is available to discuss how IronNet can detect both known and unknown behaviors.
To learn more and schedule a demo, please visit Request a Demo for more information.
.png)
