Without question, there has been noted fallout from rapid cloud migration. Gartner estimates that by 2022, Cloud Security Provider (CSP) customers will be at fault for at least 95% of cloud security failures. As the Gartner analyst Kasey Panetta explains, “The challenge exists not in the security of the cloud itself, but in the policies and technologies for security and control of the technology. In nearly all cases, it is the user, not the cloud provider, who fails to manage the controls used to protect an organization’s data,” adding that, “CIOs must change their line of questioning from ‘Is the cloud secure?’ to ‘Am I using the cloud securely?’”
With cyber criminals and nation-state adversaries waiting to pounce, no company can afford what essentially was a “cross-our-fingers” approach to cloud security during the pandemic-induced rapid migration to the cloud. Adapting perimeter defenses and on-premise controls as a quick fix will never work for either an immediate or a long-term cloud security posture. Nor can companies rely on trusted, public cloud security providers to cover cloud security for them; that onus is one shared with the enterprise.
So where do you begin?
The first step in a public, hybrid, or multi-cloud approach is clearly understanding who is responsible for cloud security — both between the enterprise and external cloud service provider(s) and between internal teams and stakeholders.
CSP shared responsibility models
Externally, Cloud Service Providers such as AWS and Microsoft publish shared responsibility models to ensure a joint approach to security that allows the ownership of data and identities to remain in the realm of the enterprise (or tenant). The CSPs, however, are responsible for securing their cloud infrastructure, including the operating system and physical access protection of their data centers — not what's "in" the cloud.
 Azure Shared Responsibility Model
Azure Shared Responsibility Model
 AWS Shared Responsibility Model
AWS Shared Responsibility Model
While there are nuances based on the provider and business-specific service needs, what does transcend the specifics of any CSP’s models is the underlying premise that the security “of the cloud” falls on the CSP’s shoulders, whereas the responsibility of securing assets and data “in the cloud” falls on the enterprise itself.
Remember this: the security “of the cloud” falls on the CSP’s shoulders, whereas the responsibility of securing assets and data “in the cloud” falls on the enterprise itself.
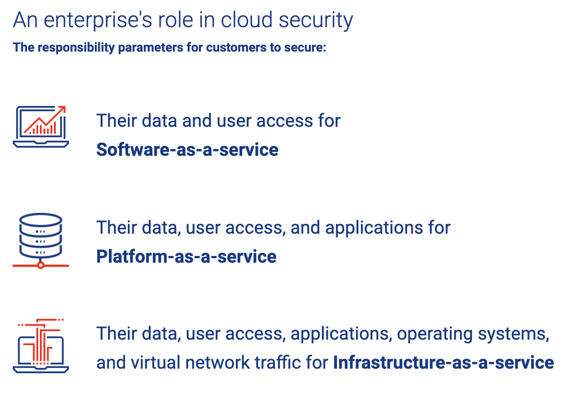
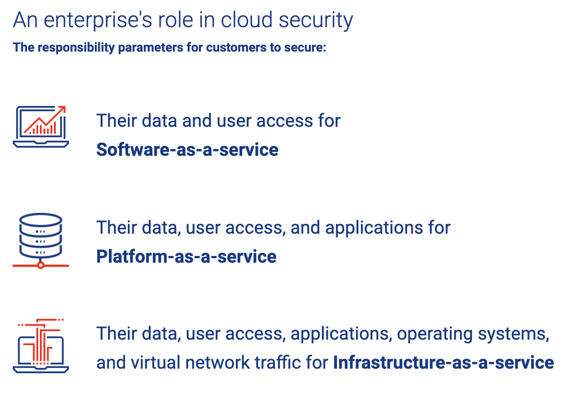
The enterprise's role in cloud security
From an internal accountability standpoint, cloud security responsibilities can vary depending on your enterprise’s cloud service model, whether software-as-a-service (SaaS), platform-as-a-service (PaaS), or infrastructure-as-a-service (IaaS):
After mapping out responsibilities in accordance with cloud service agreements, the next step is deciding who owns cloud security within the enterprise. The answer isn’t always clear, especially where multi-cloud environments are at play. Some cloud security tasks can be assigned to traditional security teams, while others such as protecting cloud data requires a certain expertise.
Strive for clarity by mapping out a cloud security RACI to ensure that data protections are not compromised by internal confusion among IT leaders, application development stakeholders, and, in some cases, line of business managers. This policy must extend to the supply chain, especially after unexpected rapid cloud migration, which may have necessitated some business functions to extend infrastructure access to third parties never intended to have access in a pre-pandemic environment.
All major CSPs have gone to great lengths to secure their cloud services — as they have done with proven success. It's essential to advocate internally for the secure use of these services, with the clear of shared responsibility models, to realize the many benefits of the cloud: scalability, agility, efficiency, improved user experiences, and reduced cost.
To learn more about cloud security, see "Cloud (in)security: Your guide to stronger cloud security with NDR."


.png)