In our mission to transform cybersecurity through Collective Defense, we are pleased to announce our technology partnership and integration with leading endpoint protection provider CrowdStrike. This powerful combination allows organizations to apply the unique capabilities of both platforms together to see more broadly across the cyber threat landscape — and more effectively defend against cyber attacks.
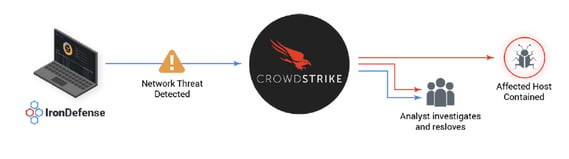
IronNet’s network detection and response (NDR) platform, IronDefense, now integrates with CrowdStrike’s Falcon Endpoint Protection capabilities. This integration extends IronNet's Collective Defense capabilities to the endpoint, providing customers with expanded visibility into potentially malicious behaviors across both networks and endpoints — while greatly increasing the speed and efficiency of response and remediation for security analysts.
The joint solution builds upon IronNet's Collective Defense communities, where organizations within an industry sector, supply chain, state, country, or other grouping, share real-time, anonymized threat intelligence insights to defend against threats targeting the community.
Don Closser, IronNet’s Chief Product Officer, said, "Integrating CrowdStrike’s capabilities for endpoint monitoring with IronNet’s ability to detect anomalies deep into the network, and in the cloud, dramatically increases the level of visibility and contextual data that our customers receive within their Collective Defense communities. The more data about potential attacks they can receive and share, the more effectively they can defend.”
IronNet and CrowdStrike integration
The CrowdStrike integration with IronNet’s Collective Defense platform enables customers to:
- Easily view network and endpoint telemetry data on a single pane of glass: IronDefense works natively with CrowdStrike to provide relevant host details through IronDefense’s IronVue User Interface, delivering the necessary contextual information that speeds up time to detection by reducing investigative workflow complexity.
- Instantly contain threats: Analysts using IronDefense can contain endpoints with one click through IronNet’s IronVue interface. This enables security teams to instantly stop threats during an investigation.
- Pivot seamlessly from network to endpoint during an investigation: IronDefense users with CrowdStrike permissions can pivot to the CrowdStrike Falcon interface for deeper investigation, allowing security teams to seamlessly trace suspicious behaviors on the network to the source endpoint.
Why add network detection and response to your cybersecurity ecosystem?
Network detection and response based on behavioral analytics can spot threats that have infiltrated the network and gone undetected by signature-based tools. These are the threats by adversaries who have managed to slip past a firewall and/or taken advantage of an insecure endpoint to get inside the network. Once inside, adversaries often dwell on the network to determine the best way to steal or manipulate data, including personally identifiable information (PII) or intellectual property. They may then move laterally across networks from their entry point to find the systems or data they are targeting.
Network Detection and Response solutions complement the firewall and EDR tools such as CrowdStrike’s Falcon Endpoint protection to catch these network threats, which don’t have traditional security “calling cards" or signatures. Occasionally, the attacker could even be an insider, such as an employee who has been given access to your network.
Either way, organizations must have the capabilities to identify suspicious behaviors on the network to stop them “left of boom,” or, in a worst case scenario, as the adversaries start to move laterally across the network. The goal is to respond before they successfully capture the intended payload or take over critical systems remotely. And if they do reach this point (or have progressed along the intrusion path), cyber defenders need a reliable way to detect that the dire adversarial techniques are in play on the network.
Download the solution sheet to learn more about the IronNet and CrowdStrike partnership.

.png)