IronNet provides more than 15 analytics in its IronDefense platform to help customers identify both common and sophisticated cyber threats. These analytics are specifically designed to find malicious behavior that are not detected by a typical signature-based security solution. Here we will run through a recent finding highlighting our Suspicious File Download analytic.
The Suspicious File Download analytic attempts to determine malicious file downloads that occur over HTTP. This means IronNet is specifically looking to identify downloads that are unexpected, from untrusted sources, and have a malicious nature to them. IronNet includes enterprise network trends and historical data to weed out most of the noise. This is a key analytic to identify possible attacks in the Initial Access phase of the Mitre ATT&CK Matrix.
In this instance, IronNet was able to identify software posing as a legitimate mapping executable, and threat hunters were able to quickly notify the customer’s enterprise security team of the threat.
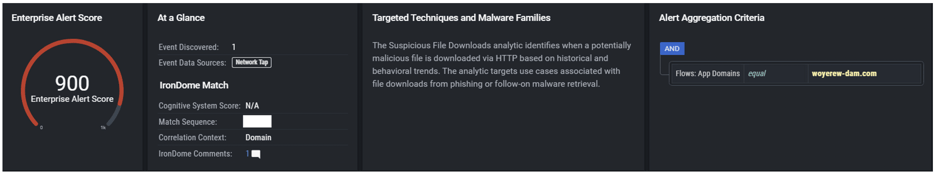
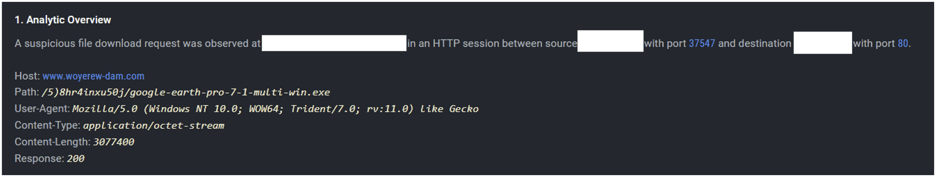
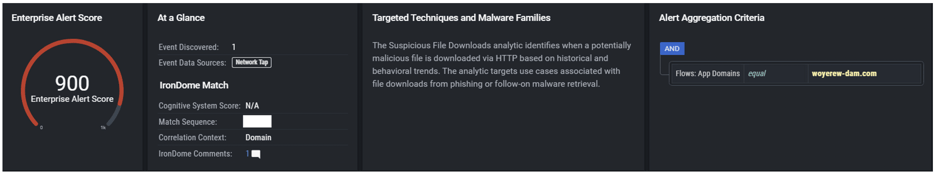
Let's take a look at an example IronDefense Alert:
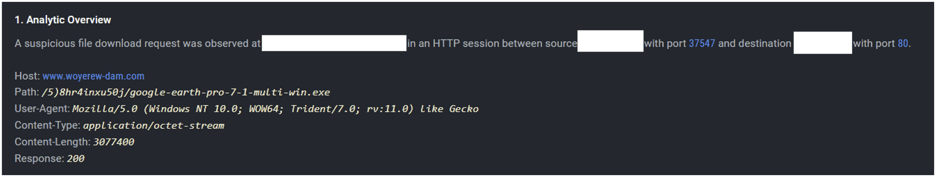
In the alert, we can see that there was a download from the domain woyerew-dam[.]com and specifically for the google-earth-pro-7-1-multi-win.exe file. We can also ascertain that the file was in fact downloaded by the HTTP Response code of 200.
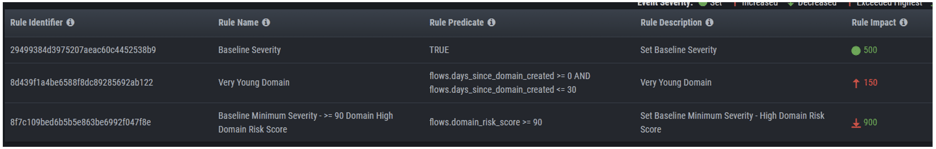
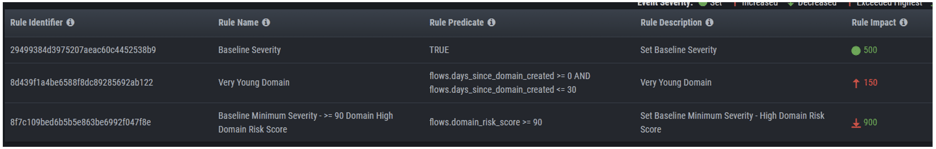
IronNet uses its Expert System Rules to provide additional enrichments to the data in an attempt to automate some of Tier 1 SOC analyst functionality. In this case Suspicious File Downloads identified that the domain in question was a very young domain and the domain was attributed a high risk score from additional threat intelligence enrichments. These scores in total allow the alert to be scored at a critical level and placed at the top of the queue for SOC Analysts.
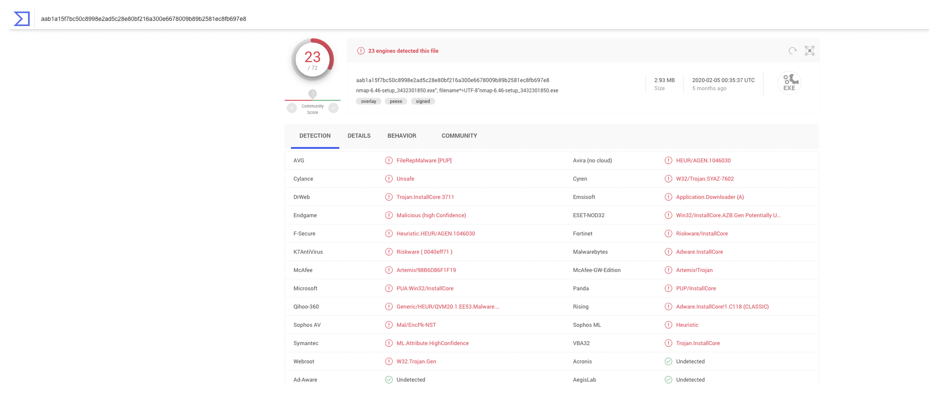
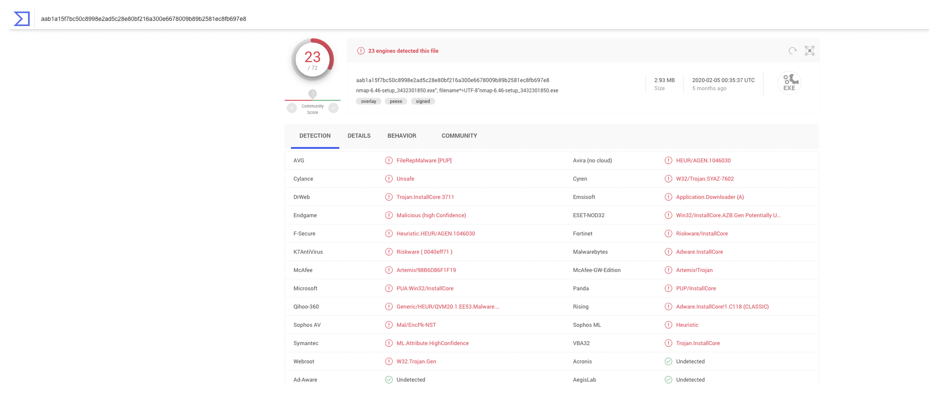
The file itself is masquerading as a Google Earth executable. As we can see below, by performing some research using OSINT sources we are able to identify that the file has an extremely poor reputation and is marked as malicious by numerous security vendors.
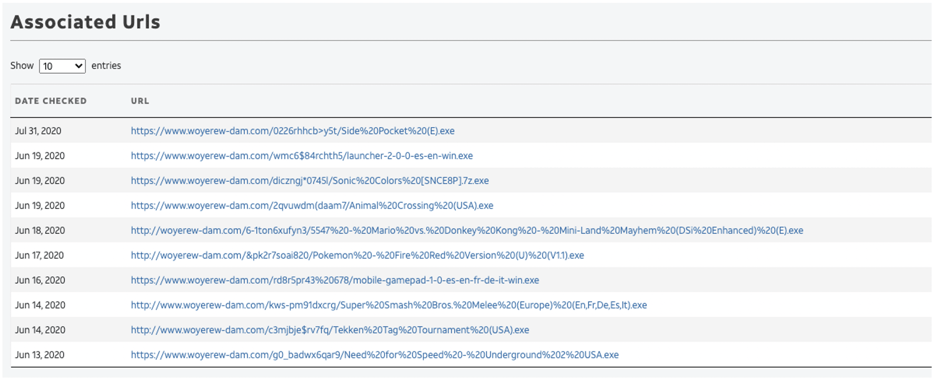
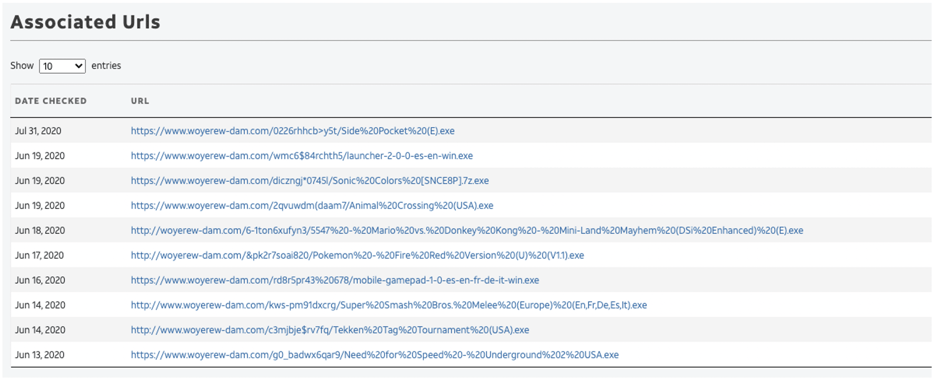
We are also able to identify that this website has been seen hosting multiple different files, ranging from game downloads to other PUP/PUA (potentially unwanted programs/potentially unwanted applications):
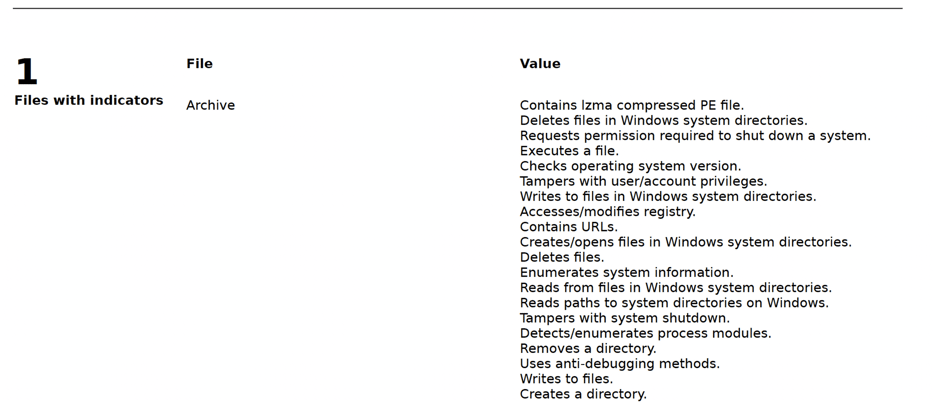
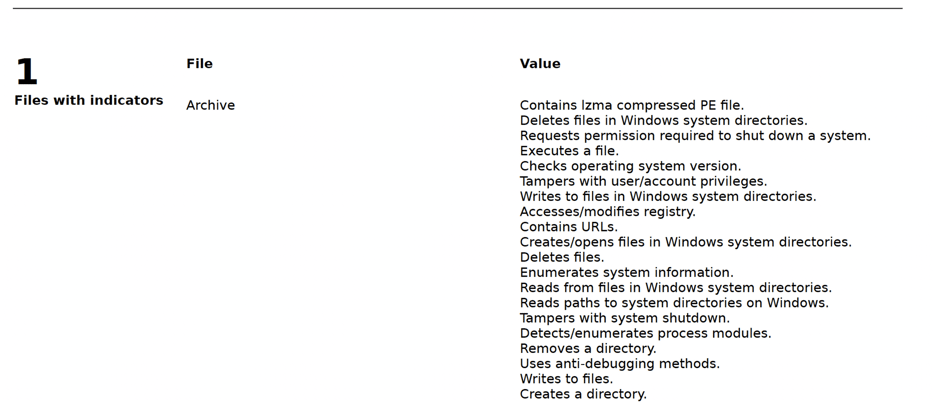
While this executable has been identified by many as being malicious, some additional analysis also yielded that the file was able to affect multiple parts of the system by modifying registry values, tampering user account privileges, creating directories, and more system modifications.
Contributing to Collective Defense
After analyzing the information within the Suspicious File Download alert, we identified that the executable was able to traverse the network proxy, and be downloaded. IronNet threat hunters then rated the activity as malicious. While we were able to quickly identify this file as malicious, there may be other instances where the file in question is more nefarious and not publicly known. By finding malicious activity using our Suspicious File Download analytic, we can then push that information to IronNet’s Collective Defense platform, IronDome. IronDome would provide immediate notifications (with minimized data) of the new threat and identify any traffic that may have been seen in the other participating customer networks. If any future activity occurs, the context from the activity is shared allowing quick response and saving critical threat hunting time with context provided.
.png)